Digital World – The Current Scenario
In the Digital connected world where data accessibility ease has enabled greater flexibility & efficiency; its privacy and security are the rising concerns. As IT systems proliferate to support business processes, users and system administrators are facing an increasingly complicated interface to accomplish their job functions. Users typically have to sign-on to multiple systems, necessitating an equivalent number of sign-on dialogues, each of which may involve different usernames and authentication information. System administrators are faced with managing user accounts within each of the multiple systems to be accessed in a co-ordinated manner in order to maintain the integrity of security policy enforcement.
Catch up with the Digitized World
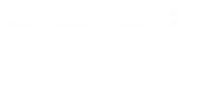
Wouldn’t it be wonderful if resources could be accessed without any interruptions using only one credential which would authenticate and authorize identities based on user roles anytime, anywhere. Secured role based access has issues which can be addressed by OpenAM – an Open Source Access Management which includes Authentication, SSO, Authorization and Federation with web services security in a single unified product. Secured OpenAM can give customers not only context-aware single sign-on access but also a personalized experience on any digital channel, whether a mobile device, connected car or home appliance.
Integrating OpenAM with Open Source Portals & ECM Solutions
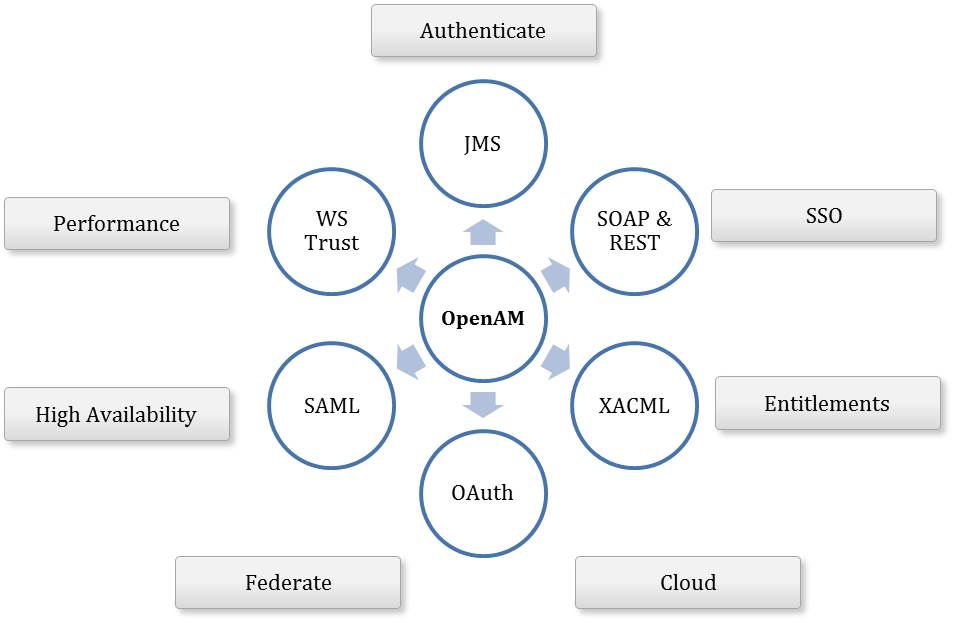
Access Management has a key role within the Portals & ECM Solutions as users have to be authenticated via multiple authentication mechanisms against different systems & scenarios. Thus users logging in from anywhere will be able to have personalized services and obtain authorization to access protected remote resources. The OpenAM functionality for Portals & ECM Solutions involves the deployment of Access Management System and implementation of authentication, authorization and logic to manage users, groups, roles & access control.
Authentication Flow
Liferay based Portals & OpenAM
Liferay is an enterprise solution primarily used to power intranets, extranets, internal collaboration sites, social community sites, consumer facing websites & customer and self-service portals. Access Management is a key feature of the Enterprise Portal that eases user interaction with many component systems available to the user in a portal environment. Once the user is authenticated to the enterprise portal, he/she can use the portal, to access external applications. With SSO in the Enterprise Portal, the user can access different systems and applications without having to repeatedly enter his or her user information for authentication.
Excerpt
open.sso.auth.enabled=true
open.sso.login.url=http://openam.local.com:8080/OpenAM-11.0.0/UI/Login?realm=Axalta&goto=h… open.sso.logout.url=http://openam.local.com:8080/OpenAM-11.0.0/UI/Logout?realm=Axalta&goto=… open.sso.service.url=http://openam.local.com:8080/OpenAM-11.0.0
open.sso.screen.name.attr=uid open.sso.email.address.attr=mail
open.sso.first.name.attr=givenname
open.sso.last.name.attr=sn open.sso.logout.on.session.expiration=false
Alfresco based ECM Solutions & OpenAM
Alfresco - Open Source alternative for Enterprise Content Management (ECM), providing Document Management, Collaboration, Records Management, Knowledge Management, Web Content Management, and Imaging. Alfresco & OpenAM are integrated using J2EE agent which enables the user to login without passing through CMIS interface.
Excerpt
<connector>
<id>alfrescoHeader</id>
<name>Alfresco Connector</name>
<description>Connects to an Alfresco instance using header and cookie-based authentication</description>
<class>org.alfresco.web.site.servlet.SlingshotAlfrescoConnector</class>
<userHeader>X-Alfresco-Remote-User</userHeader>
</connector>
<endpoint>
<id>alfresco</id>
<name>Alfresco - user access</name>
<description>Access to Alfresco Repository WebScripts that require user authentication</description>
<connector-id>alfrescoHeader</connector-id>
<endpoint-url>http://localhost:8380/alfresco/wcs</endpoint-url>
<identity>user</identity>
<external-auth>true</external-auth>
Benefits
- Reduction in the time taken by users in sign-on operations to individual domains, including reducing the possibility of such sign-on operations failing
- Improved security through the reduced need for a user to handle and remember multiple sets of authentication information
- Reduction in the time taken, and improved response, by system administrators in adding and removing users to the system or modifying their access rights
- Improved security through the enhanced ability of system administrators to maintain the integrity of user account configuration including the ability to inhibit or remove an individual user’s access to all system resources in a co-ordinated and consistent manner
To know more checkout on our IRM Expertise